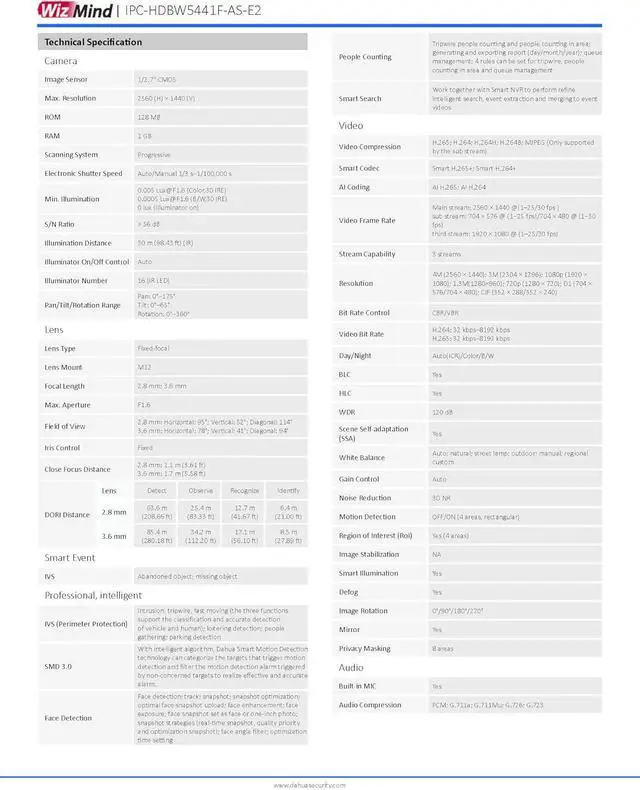
[SMD 3.0] can categorize the targets that trigger motion detection and filter the motion detection alarm triggered by non-concerned targets to realize effective and accurate alarm.
[Perimeter Protection] technology can recognize human and vehicle accurately.
[People Counting] technology can track and process moving human body targets to realize the accurate statistics of enter No., leave No., and In Area No. Working with management platform, it outputs reports to meet your requirements.
[Face Detection] technology supports detecting, tracking, capturing, and selecting the best face image, and then outputs face snapshot.
[Cyber Security] technologies employ security authentication and authorization, access control protocols, trusted protection, encrypted transmission and encrypted storage.